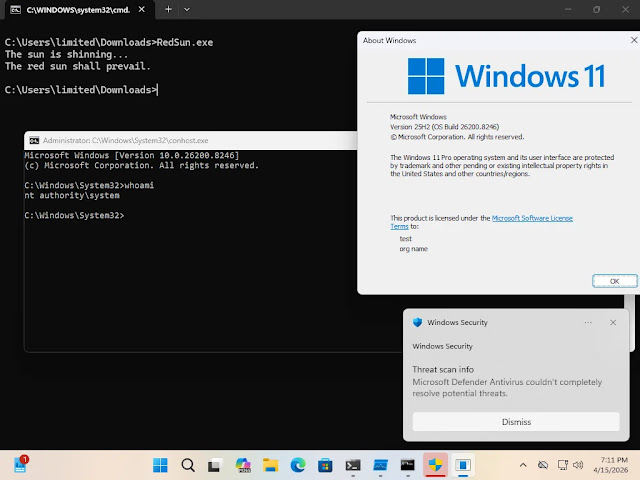
The newly discovered zero-day vulnerability known as "RedSun" in the Microsoft Defender platform poses a serious threat to Windows users. This flaw allows an attacker with standard user privileges to achieve SYSTEM-level privileges on the affected system.
According to researches, the "RedSun" vulnerability can affect Windows 10, Windows 11, as well as Windows Server 2019 and later versions. The root cause of the vulnerability is a logic flaw in the file remediation mechanism located in MpSvc.dll, which is the core Malware Protection Engine component of Microsoft Defender. When Defender detects a malicious file carrying Cloud Files attributes (“cloud-tagged”), it attempts in certain cases to restore the file back to its original detection path. However, during this write operation, it does not verify whether the target directory has been redirected to another system directory through a junction point. The attacker exploits this exact weakness.
The exploit chain leverages the following legitimate Windows mechanisms:
According to the analysis, as a result of successful exploitation, the attacker-controlled file is placed into “C:\Windows\System32\TieringEngineService.exe” with SYSTEM privileges. It is then executed through the Storage Tiers Management COM Server invoked via CLSID {50d185b9-fff3-4656-92c7-e4018da4361d}, resulting in the attacker obtaining a SYSTEM shell. This process requires neither administrative privileges, nor UAC bypass, nor a kernel exploit.
Researchers have reported that the "RedSun" vulnerability has already been observed in real-world attacks. According to their findings, attackers placed the exploit files in user directories, including the Pictures and Downloads folders and renamed them to avoid suspicion. They then performed initial reconnaissance on the system using commands such as whoami /priv, cmdkey /list and net group.
At present, there is no official security patch available for the RedSun vulnerability. Therefore, users are strongly advised to regularly monitor Windows security updates, watch for unusual system activity and implement additional security measures where possible.
© 2011-2026 All rights reserved