The security update released for Microsoft Defender caused two legitimate DigiCert root certificates (DigiCert root certificates) to be incorrectly identified as malicious. As a result, it introduced a risk of disruption to SSL/TLS validation and code-signing verification processes across enterprise environments.
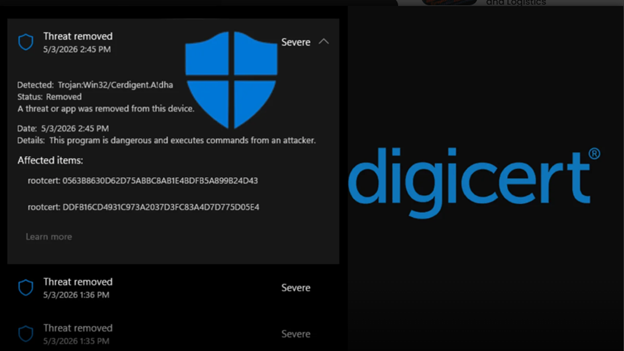
According to available information, an antimalware signature update released on April 30, 2026, triggered a detection labeled “Trojan:Win32/Cerdigent.A!dha”. This detection incorrectly classified registry entries associated with the “DigiCert Assured ID Root CA” and “DigiCert Trusted Root G4” certificates, stored in the Windows trust store, as high-severity malware.
These certificates reside in Windows systems under the registry path HKLM\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates, where trusted root and intermediate certificate authorities are managed. On affected systems, Microsoft Defender automatically quarantined these entries as part of its standard remediation workflow, effectively removing them from the Windows trust store.
This situation created a particular risk for organizations relying on DigiCert-signed software and HTTPS resources. The absence of these root certificates could prevent proper SSL/TLS validation for websites, trigger browser warnings, disrupt code-signing verification for legitimate software and lead to service interruptions across enterprise networks.
Microsoft acknowledged the issue and released corrected signature updates. It is reported that version .430 served as a key fix, restoring the quarantined certificates on affected devices.
© 2011-2026 All rights reserved