In recent years, trends observed in the field of cybersecurity indicate that threat actors are increasingly moving away from traditional attack methods and adopting more indirect techniques that rely on user behavior. In this context, one of the most notable emerging approaches is QR code-based phishing attacks, commonly referred to as “quishing”. This method is considered an evolved form of conventional phishing campaign and has gained a more dangerous dimension with the widespread use of mobile technologies.
In traditional phishing attacks, users are typically sent malicious links and are expected to click on them. However, due to advancements in security mechanisms and increased user awareness, the effectiveness of such attacks has declined to some extent. As a result, attackers have begun to explore alternative vectors, with QR codes emerging as an effective tool in this regard.
Since QR codes are perceived as visual elements, they are often regarded as inherently trustworthy by users. Moreover, when scanning a QR code, users do not typically analyze the underlying URL beforehand. This provides attackers with a significant advantage from a social engineering perspective.
Attack Mechanism
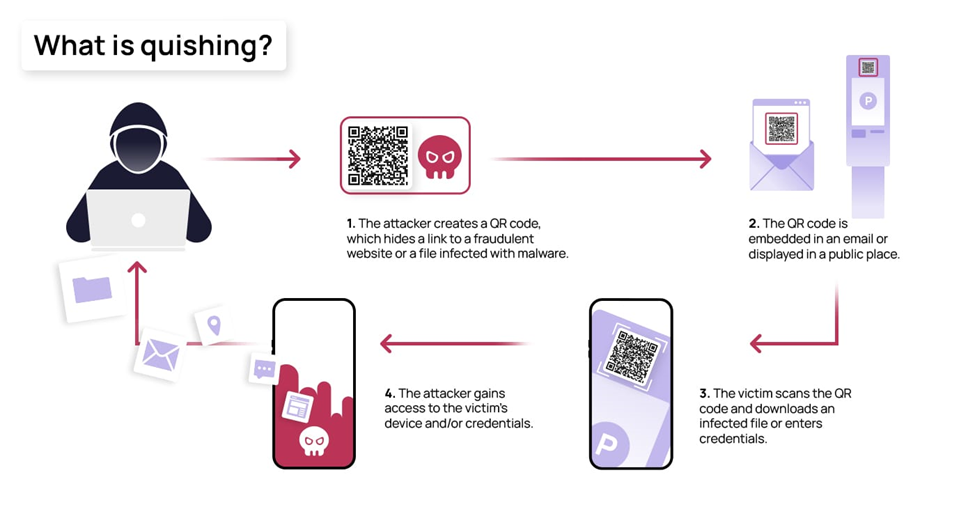
Quishing attacks typically begin with social engineering elements. Users are presented with QR codes through various channels, including SMS messages, emails, social media platforms or even physical media such as stickers placed in public environments. These QR codes are often embedded within contexts that imitate official institutions or trusted services to reduce suspicion.
Once the QR code is scanned, the user is taken through a multi-stage process. In the initial stage, a CAPTCHA or a similar verification mechanism is commonly displayed. This serves a dual purpose: it enhances the perceived legitimacy of the interaction for the user and helps bypass automated security analysis systems. Subsequently, the user is redirected to a fraudulent webpage designed to closely mimic legitimate services. On these pages, users are prompted to enter sensitive information such as login credentials, banking details or other personal data.
In some cases, the attack is structured as a more complex chain. The user may first be directed to an intermediate page and then redirected multiple times before reaching the final malicious destination. This layered redirection makes it more difficult for security tools to trace and analyze the attack flow.

Research indicates that the technologies used in such attacks are increasingly sophisticated. QR codes are often linked to dynamic URLs that can be modified in real time. This capability allows the attack to remain active for extended periods and complicates detection efforts.
Collectively, these features not only enhance the realism of the attack but also help evade detection by conventional security systems.

Recent campaigns indicate that quishing attacks are carried out in a variety of forms. For instance, users may receive messages claiming that they have an unpaid fine, accompanied by a QR code for payment. In other cases, notifications are sent under the guise of postal or delivery services, prompting users to scan a QR code to access further details.
One of the more concerning variants involves attacks conducted in physical environments. In such scenarios, threat actors place malicious QR codes in public locations, including parking meters, restaurant menus and advertising boards, thereby deceiving users. In these cases, individuals may not even realize that they have been exposed to a malicious interaction.

Overall, QR code-based phishing attacks are increasingly regarded as a new and significant trend in the cybersecurity landscape. This approach effectively combines technical techniques with social engineering tactics, exploiting user trust. Current developments suggest that cybercriminals are adopting increasingly creative and indirect methods to obtain sensitive information.
© 2011-2026 All rights reserved