A new attack technique targeting the macOS operating system has been identified. According to the information, attackers attempt to evade traditional detection methods by hiding malicious code within the system’s Spotlight metadata mechanism.
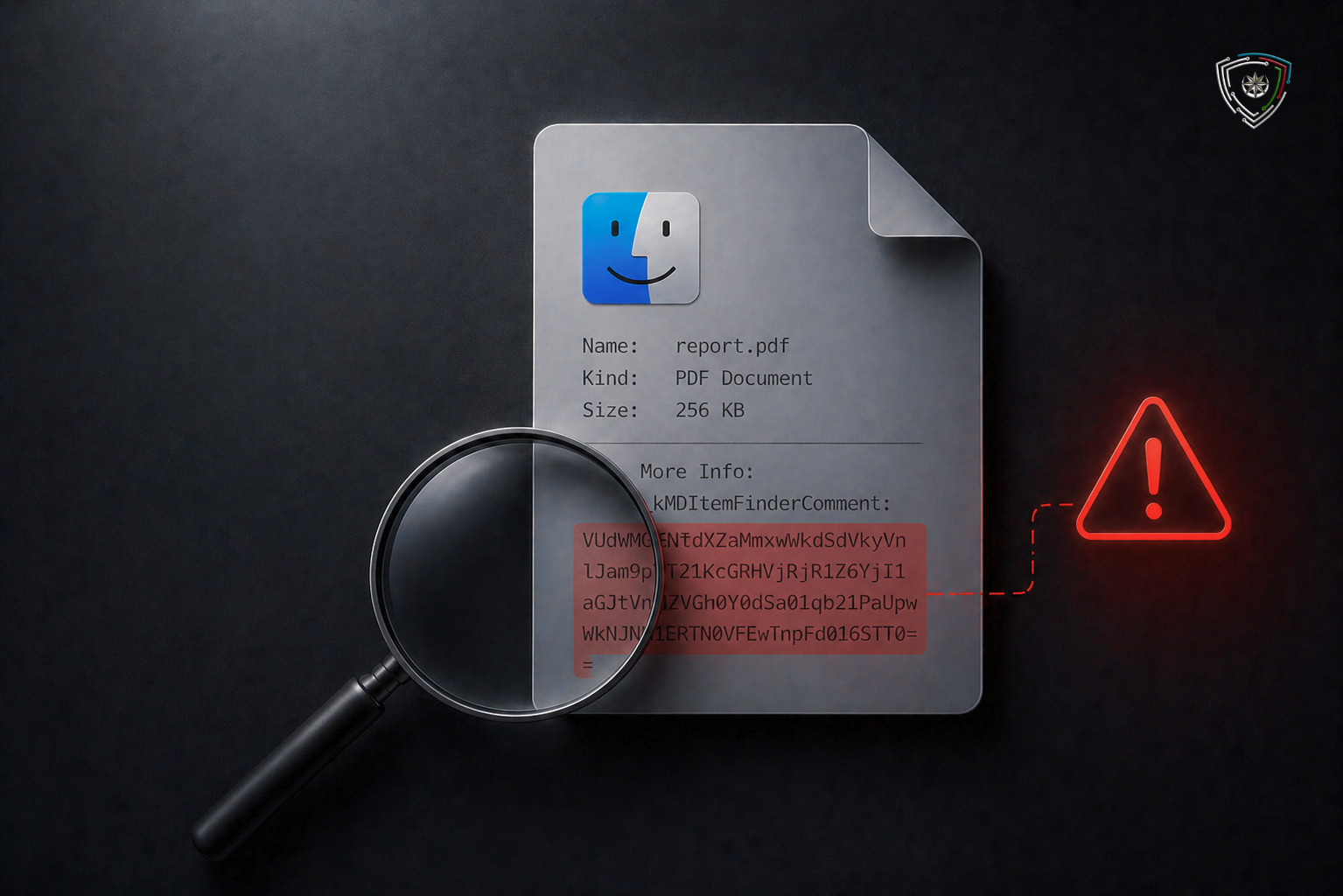
The malicious payload is reportedly stored in Spotlight metadata, specifically within the Finder Comment field and the “kMDItemFinderComment” metadata attribute. The payload is first Base64-encoded and then embedded into the file’s metadata. As a result, the malicious content does not appear in the file’s main body, making it considerably more difficult for static file analysis and certain endpoint security solutions to detect.
Threat actors can also abuse Remote Application Scripting (RAS) to create a file on a remote system and insert malicious content into its comment field. This process can be carried out through the “eppc://” protocol.
In addition, attackers can transfer toolkits, perform lateral movement and establish persistence by leveraging built-in protocols and utilities such as SMB, Netcat, Git, TFTP and SNMP. Since these activities operate outside the visibility of standard SSH-based telemetry, they can significantly limit the detection capabilities of security teams.
This method is considered a dangerous example of the “Living-off-the-Land” approach in macOS environments. Experts emphasize that organizations should not rely solely on file-based detection for macOS devices, but should also monitor metadata changes, unusual script executions, remote application management and suspicious use of built-in protocols.
© 2011-2026 All rights reserved